use this cheatsheet to your advantage, you may want to look for dennis.
- once cracked the password for the docx. Is there any docx friendly applications out there? Maybe google drive?
- use the hint and the juicy stuff you find in there to your advantage
- get familiar with mysql
- once you ssh as that user… what can you find?
- how would you crack this?
i can not get in the doc. I have tried with google drive but it is asking me for pass
you have to crack it and use a john tool. Look back in the module of some of the tools that are compatible with the doc.
I have done it, it wasy trickier than hard lab
I found this lab to be quite tricky as well. For those that need a hint, look at the sections under “Remote Password Attacks”. There is a section there that explains one particular point about this lab.
Can’t remember the cartoon you have on your profile picture,but it was the funniest stuff i watched. And thanks, just by asking questions you made me understand better.
when you ran John did it instantly finish?
When I keep running it with different password list it doesn’t run
yes, mut password will solve
I don’t believe it instantly finished for me. Maybe the ‘passwords.txt’ won’t wrok for this. What about the mutated password list?
This is Easy Box But need to think before doing things ![]()
- get jason from doc
- get dennis from mysql
- dennis key is root ssh
Follow these steps
- Download creds from resources and create mutated password list.
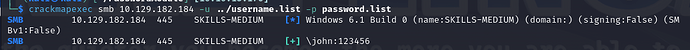
- Using crackmapexec crack smb creds(hint :- use normal creds not the mutated one for faster cracking)
- Download Docs.zip file using get filename command.
- using zip2john.py conver zip into hash.
- crack the converted hash using john and password list ( if the password list doesn’t work then use the mutated one)
6.Next you need to convert doc in to hash using office2john.py - crack the above hash.
- install the libre office to read the document which is protected.
- you will find the creds in doc. login with those.
- use mysql --host=localhost --user=jason --password=“password_you_found”
- read the database and you will user named “dennis” and his password.
- login with other user creds.
- you will find root ssh private key in dennis folder .
- convert it to hash with ssh2john.py and the crack it with mutated passwordlist.
- then login with the user root using ssh root@ip -i id_rsa and enter passwd you found( Don’t forget to change perm of Id_rsa [chmod 600 id_rsa])
<<<<>>>>>
Thank you for reading this, I hope it helped you.
Old thread but don’t forget that people reuse passwords and don’t forget the ; at the end in an important command that is being suggested from the document
you need to follow these steps above of Vision. when access mysql use creds database and using command “select * from ‘table_database’;”
Hello,
I try to start this Medium assessment and I don’t even succeed to get a single entry point.
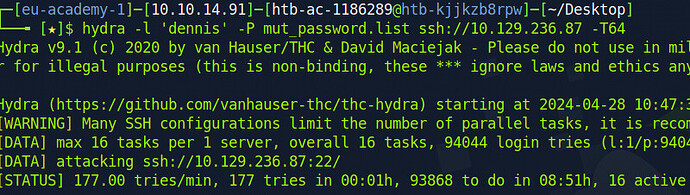
I try some login with the mut_password but it’s 9h long, and I don’t even know if my login nor my protocol is good.
Can someone could give me a hint to get my first entry point or to tell me how I can speed up the bruteforcing ?
Thank you for your help
I upload a printscreen of the example of command I launch.
You may not want to bruteforce the ssh directly with user dennis. There is other service running on the machine. You may want to brute force this service using the resource provide by HTB (user list and password list). Good luck.
Thank you for the reply.
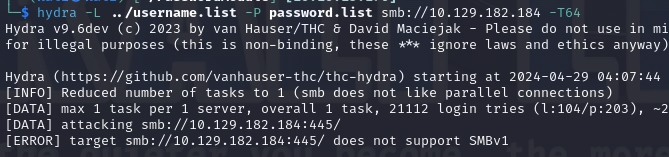
But I can’t succeed to hydra the smb service
I have this error message: [ERROR] target smb://10.129.182.184:445/ does not support SMBv1
I tried to do the same thing like explained in the * Password Attack - Network Services*.
I even tried to reinstall hydra but without success.
I don’t see other network service on the machine.
I tried to use crackmapexec and it seems to retrieve the login john with the password 123456 (as per my screen capture)
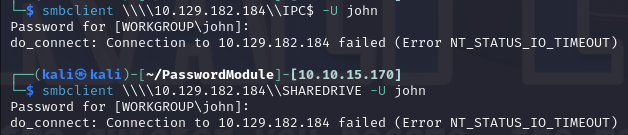
I can’t use it to do anything with SmbClient
I am not really comfortable with SMB
I know I am missing something under my nose but I can’t see what.
You did cracked the samba password. Next step is to get a file from this samba share. You cannot connect to the samba since you were using a command to connect to windows smb share. This is Linux box so the directory use different slash.
@lv715 Thank you a lot.
You made me succeed this assessment <3
I’m stuck in the point 9 ![]() I can’t connect to mysql database, I think that I’m doing something wrong
I can’t connect to mysql database, I think that I’m doing something wrong ![]() help me please!
help me please!
pd: I already had access to ssh with Jason