More information:
curl -X POST IP:PORT/login.php --user “test:test” returns the html i used for the F string. Wasnt seeing any results so i changed the F string from the provided “<form name=‘login’” to “‘login’ autocomplete” just to be safe about the additional ‘=’ in the string. I used curl because when attempting a login using bad credentials in the browser nothing is returned except for a 403 (forbidden) status, and you are brought to a white page. However when attempting the same request using curl you do get a response.
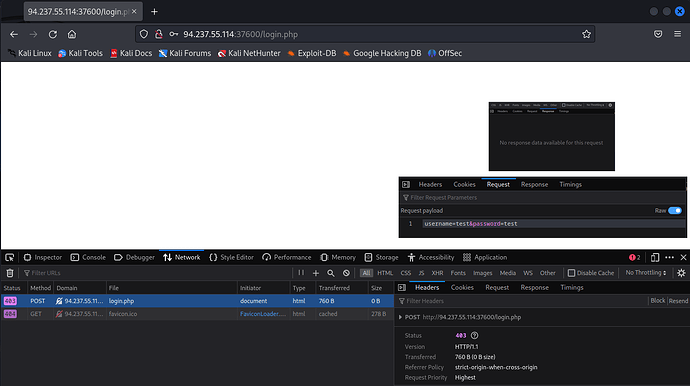
Images of attempt using browser (sorry about editing together, cannot submit more than one attachment):
curl command & response:
curl -X POST 94.237.55.114:37600/login.php -v --user "test:test"
* Trying 94.237.55.114:37600...
* Connected to 94.237.55.114 (94.237.55.114) port 37600 (#0)
* Server auth using Basic with user 'test'
> POST /login.php HTTP/1.1
> Host: 94.237.55.114:37600
> Authorization: Basic dGVzdDp0ZXN0
> User-Agent: curl/7.88.1
> Accept: */*
>
< HTTP/1.1 200 OK
< Date: Wed, 19 Jul 2023 00:48:27 GMT
< Server: Apache/2.4.41 (Ubuntu)
< Set-Cookie: PHPSESSID=tmld0nob3ju3bi9jqaipp1ojn7; path=/
< Expires: Thu, 19 Nov 1981 08:52:00 GMT
< Cache-Control: no-store, no-cache, must-revalidate
< Pragma: no-cache
< Vary: Accept-Encoding
< Content-Length: 1538
< Content-Type: text/html; charset=UTF-8
<
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Admin Panel - Login</title>
<link rel="stylesheet" href="./style.css">
</head>
<body>
<form name='login' autocomplete='off' class='form' action='' method='post'>
<div class='control'>
<h1>
Admin Panel
</h1>
</div> … Continues.
Passlists used ordered by their respective directories:
SecLists/Passwords/LeakedDatabases/
000webhost.txt: Times out, no results
bible.txt: Completes, no results
elitehacker.txt: Completes, no results
hak5.txt: Completes, no results
honeynet.txt: Times out, no results
honeynet2.txt: Times out no results
phpbb.txt: Times out no results
rockyou-75.txt (& below): Completes, no results
rockyou.txt: Times out, no results
tuscl.txt: Completes, no results
SecLists/Passwords/Common-Credentials/
10k-most-common.txt: Completes, no results
10-million-password-list-top-10000.txt (& below): Completes, no results
10-million-password-list-top-100000.txt (& above): Times out, no results
100k-most-used-passwords-NCSC.txt: Times out, no results
500-worst-passwords.txt: Completes, no results
best1050.txt (& below): Completes, no results
SecLists/Passwords/Default-Credentials/
default-passwords.txt: Completes, no results
combined all the betterdefaultpasslist.txt files using grep and tried a combined credentials attack using the combined & sorted file: Completes, no results
SecLists/Passwords/Cracked-Hashes/milw0rm-dictionary.txt: Times out, no results.
Do they want us to find other wordlists from other repos? Surely not? Im just trying to follow the content provided and cant seem to get anywhere. Would love some input. Cheers!
-F