hey i am doing the updated module of attacking common apps and i am now in fatty and i get admin but i get incorrect answer when i enter the content of uname what am i doing wrong? that what i got Lin****
Linux 03dcd3e5e277 4.9.0-11-amd64 #1 SMP Debian 4.9.189-3+deb9u1 (2019-09-20) x86_64 Linux
This is what I got too.
I guess @admins @moderators need to check this out.
you guys need to select ipconfig/ifconfig, instead of the first option shown in the screen shot if i remember correctly
For some reason, I get to the point where I create the fatty-client-new.jar and when I double click it, nothing happens. I followed the process of removing the hashes and modifying the beans.xml file with the port 1337 as indicated in the lesson. Does anyone know why this doesn’t work?
Hi, same problem here. Even can’t scan the app connections with wireshark. Did you solve it?
Same problem…
Even when lanuched the connect button dont work at all.
Solution found: Don’t make any changes to the MANIFEST.MF. Rest of the steps are the same.
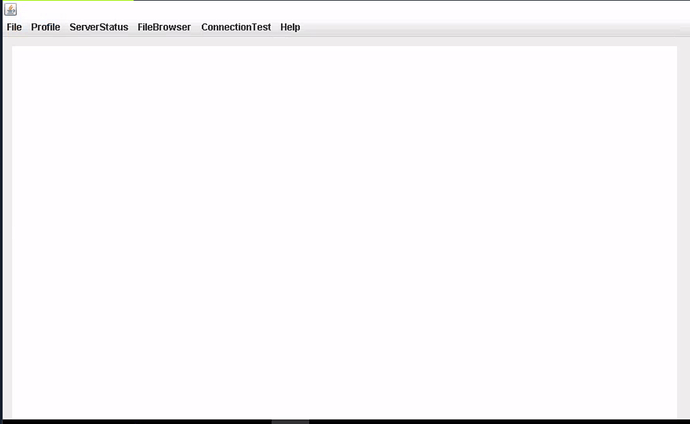
Anyone finished this module, I have been stuck for a long time… my java application does not show the lower bar so I cant open any files…
I try to complete the module following the guidelines but I am missing steps if I cant open files in the java application…
do you find bar
did you manage to sort this?
my button isnt working too!
dw i got it
forgot to delete the 2 files when recompiling it XD
Did you manage to solve the last question? I am following the same steps given but the fatty-server.jar is not showing in Config Tab
“What is the IP address of the eth0 interface under the ServerStatus”
Just a minor detail I found very helpful when trying to get the jar file running after the MANIFEST was altered… Its crucial to also delete the .RSA and .SF files from the MANIFEST-directory… Otherwise the jar will still try to find all the hashes for the class-files and the jar will not run. hope that helps anyone.