Rooting this box was really fun.
User : sql attack + sub**** enumeration is key concept here
Root : Basic manual enumeration for lateral movement and again basic enumeration will give the priv esce path.
hacktricks is always there with help for how to do when you know what to do…
Anyone need help dm me.
You should add --append-domain and the command will be like this:
gobuster vhost -w /path/to/bitquark-subdomains-top100000.txt -u shoppy.htb --append-domain
It works for me.
Heed @ald3rs0n 's words about enumerating your way to root here: think basic. Like, the. most. basic. thing you might do to extract information out of a file.
Overthinking it really had me tearing my hair out, and (confession), when I entered The Basic Command, it was an accidental autopilot; I was about to clear my screen and try something else, when I realised, “wait… that output looks different”…
I do not understand why I can not test with sqlmap. I just does not work. I get that
[CRITICAL] connection timed out to the target URL
I copied the request from burp! So my command looks like this
sqlmap -r shoppy_login_request.txt -p username --level 3 --risk 3
Any ideas why that does not work? I feel like its the only way to get in that mchine!!
EVEN wfuzz does not work!
Hey have you rooted the box? I think I need some help over here regarding the running services. I tried both the s** and nos** injection before but didnt seem to work for me. I’ve tried reading some writeup regarding the payloads but still dont understand how one comes up with a way to tweak the payload.
Edit: Well I think I kinda understand now after researching how the query works. Kindly DM me if you’re up for discussion
Feel free to pm me, I will add you on discord and we could discuss there ![]()
hi, do we bypass login page first then try to find the subdomain or vice versa?
because the application times out for some reason, so sqlmap is not effective. You have to find a manual way to do it.
Hi All,
I wanted to ask if someone could explain to me the SQLi vulnerability. More specifically, how to determine what to enter in the input fields. I was able to use a single character to determine there was an SQLi vulnerability, but not how to exploit it further. I found something on the internet that worked, I’m sure a few of you have, but I want to understand how the specific SQLi exploit worked.
I don’t want to just copy/paste things I find, so if anyone would mind talking me through, or providing a link, to explain how I might have found the right exploit myself, I’d really appreciate it.
Guys i am 2 steps ahead of root flag , I’m stuck between master and deploy
Nice box, didn’t require anything that wasn’t straight out of HackTricks. Good intro to a variety of techniques that you don’t often see on “easy” boxes (light RE, escaping things). Tips:
user - if you’re reading the forum, you probably know what to do, but make sure you try what you’re doing everywhere
root - once you’re the correct user, ip a and some googling should be all you need to proceed
DMs welcome
I’m so glad I finally escaped that interface ![]()
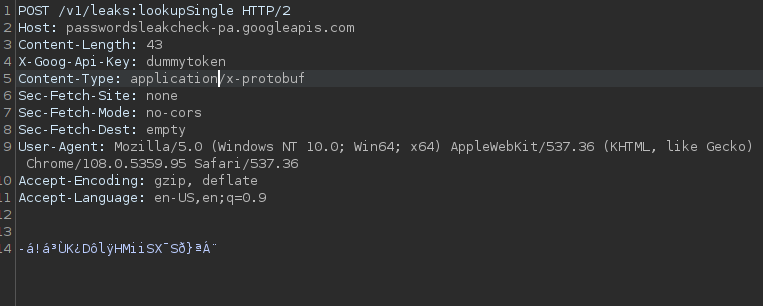
lost a lot of time debugging due to creepy google chrome security settings
if anyone got stuck check this out - https://support.google.com/chrome/thread/68814317/can-not-disable-password-leak-detection-anymore?hl=en
Hi guys, managed to root the machine , using the useful hints in here, but I was wondering how you figured out it was **SQLi / ***goDB as im reading up on the machine now and im just wondering how you guys spotted it?? Or was it through trial and error, one person said it was to do with the authorization, if someone could explain how you came to the conclusion of this, would be very helpful!
I too was unable to independently identify that the database being used was MongoDB. Like the others on this thread I tried enumerating with sqlmap and ran into the same issue of the connection timing out, which makes the scan inconclusive.
There are equivalents to sqlmap for nosql databases: check out mongomap and nosqlmap. After rooting the machine I went back and tested mongomap and found that it did indeed successfully identify that the login form was vulnerable.
In conclusion, thorough enumeration is going to be a part of any penetration test. Make sure to add the above tools to your tool list.
I don’t even have any idea how to get a foothold on this thing. I’m too busy playing around with this absolutely beautiful countdown.
Cant found the way to actually know the type or vendor of the DB, are people just bruteforcing everything? Walkthrough videos on yt are worthless since they just enter the correct payload, that is magicly comming out of h4x0r-land, the land where pentest without enumeration is possible. ![]()
Finally rooted. This one took me a long time, as there are like 5 or 6 layers from start to end.
I felt the initial enum was good practice for finding directories and subdomains. Similarly getting the foothold with a different kind of database was new to me – I had to clone a new tool that I had never used before. I also learned about md5 hashes. I enjoyed jumping from step to step figuring out what needed to be done.
My one complaint about this box is getting to the second non-privileged user. I felt that the hidden secret for this login was not at all educational. I wasted hours on this despite having cat’d the binary once at some point. This bit is not constructive and doesn’t really offer any enumeration practice other than truly look at literally every single garbled string that just might turn into something useful… which isn’t exactly realistic. Was there any way to debug this binary that I missed?
after having spent hours on that gem the root itself only took a few minutes – literally copied and pasted from the hacktricks manual for this particular vector.
all in all , I felt this was a harder “easy” box, but I enjoyed it.
sqlmap captures all types of your usual SQL DB, except for… this other kind of db. amrbekhit above mentions two tools for this and I tried both of them. One worked for me, the other did not, but simply learning how to use it and running it provided me with a working exploit and an explanation.
in the future i’ll be running both sqlmap and this other “non” sqlmap when I encounter a situation i think might require injection
Hello guys, I have a question related to initial foothold (I already got it but reading to a writeup it was not a mine result), so my question is how people get it because all the tool used did not worked (and I know to which attack the website is susceptible), can someone explain this to me? More detail in DM, thanks in advance