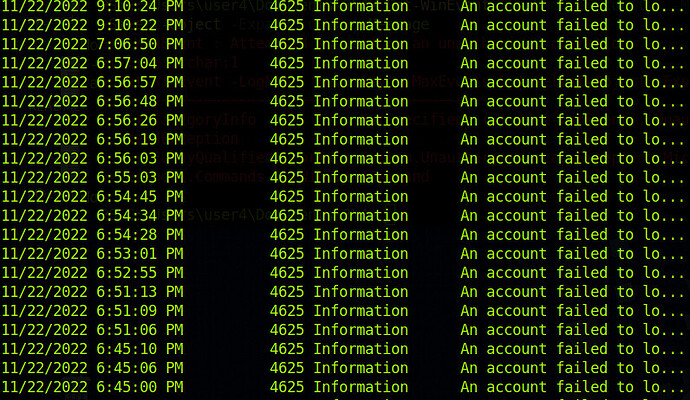
I’ve gone as far as to read all of the messages in the Event log using Get-WinEvent -FilterHashTable @{Logname=‘security’;ID=‘4265’} | select-object -ExpandProperty where I see a large number of login attempts for administrator and user0 but neither of those selections seems correct. Help would be much appreciated, thank you in advance.
After Using Get-WinEvent -FilterHashTable @{LogName='Security'; ID=;4625'} I was able to drill down
Setting variables $StartTime and $EndTime I was able to drill down using
Get-WinEvent -FilterHashTable @{LogName='Security'; ID='4625';StartTime=$StartTime;EndTime=$EndTime} | Select-Object -ExpandProperty Message
I’m given three account names that have successive log on (administrator, user0, and user1).
However none of the three are the correct answer. A little help would be much appreciated
So after a little digging and a lot of research on active directory commands in powershell I ended up counting bad password attempts Get-ADUser -Filter * -Properties AccountLockoutTime,LastBadPasswordAttempt,BadPwdCount,LockedOut
Hello GuySensel,
So I finally figured it out. You need to log into the Domain Controller after sshing to the machine which means you have ssh to 172.16.5.155 after you ssh to the regular ip address. then start look for suspicious user account name in the -expandproperty message of the failed longons.
the correct answer is (Just a little hint): ju***********admin