Solved
Hey did you end up figuring out how to do the osticket stuff? I’ve been stuck on it for hours, makes no sense how I’m supposed to get credentials.
to find the password use the typical rockyou.txt and the given rce script given, i used a While loop to iterate all the passwords of rockyou, but luckily it took seconds to find it.
If you see this after you try the exploit
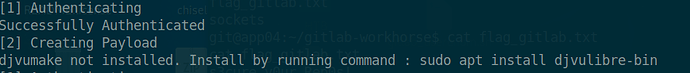
make sure to install the apt because i was iterating with that error and thats why I didnt find nothing, i installed it and just took literally 2 seconds to find it.
Who is updating the module? can’t answer the question on page 21 Attacking thick client applications due to an error on the attacked host. Doesn’t want to run Power shell. Does anyone have this?
![]() decided. if it does, run it as administrator
decided. if it does, run it as administrator
I am not able to find another valid user on the gitlab instance. I found a few but none of those are valid. I am using the python3 script to enumerate users using the biggest wordlist but still no luck. For some reason my bash script is giving me an error and I can’t fix it.
Can someone provide a hint on how to do it?
Thanks
Had some troubles too, till I realized that the username is case sensitive.
Your scan probably gave you differently cased users. One of them is the right one. ![]()
Thanks. One of them actually worked!
Hi, Is there someon that managed to get the “Exploiting Web Vulnerabilities in Thick-Client Applications” working? I am stuck recompiling the .java class with "
javac -cp fatty-client-new.jar fatty-client-new.jar.src/htb/fatty/client/gui/ClientGuiTest.java
Figured out the issue
I do not know if it varies for each time you run it. But I found it by looking first at looking at a “Map” type and “-rw–” protection. If you identify such a record, you can verify if it has the size of 3000 at the end. That should do it. It is a bit of a search but that way worked for me.
I do not know if it a viable stratagy to look at the same info headers present in the image for the module. I am not sure if that was the same for me. But maybe that can also help you.
I just figured it out, I wasn’t modifying the .bat file quick enough to capture the files. Thank you for getting back to me.
Whenver I want to use aquatone, it gives me an error about chrome (not installed). Now I’ve changed the patch with -chome-path but it still does not work. What did I do wrong?
what is the password-list for tomcat ??
i try tomcat_mgr_default_userpass.txt and tomcat_mgr_default_pass.txt
I ran into this problem also and that’s because Chrome is not installed by default on Parrot OS…
My workaround was to give Aquatone the path to Firefox instead, for instance:
cat web_discovery.xml | ./aquatone -nmap -chrome-path /usr/bin/firefox
I hope this helps.
THX
Okay, I got it. To answer the osTicket question use the credentials from the example in the module itself. You literally only have to log in as an agent and then find the ticket. You don’t have to actually exploit the SSRF vulnerability. I hate it when the authors do that but what can you do… 3 hrs of my life gone.
Could anyone tell me which wordlist I need to use for the first “Attacking GitLab” question? (“Find another valid user on the target GitLab instance.”. Been trying with some of the but the bigger lists take forever to complete?
I’m using the python script linked in the module. (GitHub - dpgg101/GitLabUserEnum: GitLab User Enumeration)
I’m currently testing xato-net-10-million-usernames.txt with no luck, even though I have found some users but they aren’t the right ones.
I’ve found:
bob
root
demo
public
help
hacker
explore
Wow I was severely overcomplicating everything ■■■■
I am stuck on the Attacking Tomcat assignment. I have found the correct user (by simply guessing on the question on HTB) and have now run atleast 5 different password lists with that user (including Xato top 100000 and about 500k lines of rockyou) but I am unable to find the correct password. I also tried two different tools: burp intruder and the metasploit module but nothing. I am unsure where to go from here. Can anyone give me a hint?
